- Introduction: Decoding Zero Trust Network Access (ZTNA)
- Why is ZTNA crucial for hospitals?
- ZTNA: The Heart of Zero Trust in Healthcare
- Implementing Zero Trust in Hospitals
- Enhanced Security and Protection For Medical Institutions
- Zero Trust in Action: No More “Open Door” Policy In Healthcare Facilities
- The Future is Now: AI Meets Zero Trust
- Cato SASE Cloud: The Digital Doctor for Hospital Networks
- Wrapping It Up: The Cybersecurity Prescription for Healthcare Providers
- 9 frequently asked questions on ZTNA for Hospitals
Introduction: Decoding Zero Trust Network Access (ZTNA)
Welcome to the world of Zero Trust Network Access (ZTNA) – sounds like something you’d hear in a Bond movie, right?
In the bustling digital corridors of hospitals, where data zips around like life-saving potions, there’s a new sheriff in town. And its name? ZTNA.
So, what’s the big deal with ZTNA? Imagine it as your cyber bouncer – tough, savvy, and not fooled by fake IDs. Gone are the days of the casual “Oh, I recognize you, come on in” approach.
In today’s world, where cyber threats are as common as coffee spills, ZTNA trusts no one; it’s all about “Show me your credentials, or no entry!”
Operating on the mantra of “Never trust, always verify,” ZTNA is like your network’s very own Secret Service, guarding every digital door and window.
It ensures that accessing your hospital’s precious data is tougher than breaking into Fort Knox. So, strap in and get ready to dive deep into the ZTNA universe – your data’s personal bodyguard!
ZTNA is also part of the larger security framework called Secure Access Service Edge (SASE) which we have written in detail in earlier articles.
Why is ZTNA crucial for hospitals?
Your hospital is a treasure trove of sensitive health data, a magnet for cyber ne’er-do-wells. ZTNA steps in as your digital knight in shining armor, protecting this treasure from the sneaky dragons of the cyber realm.
It’s all about giving the right access to the right people while keeping the bad guys out. It’s not just a security protocol; it’s your hospital’s digital immune system, always active, always vigilant.
So, as we embrace the future, ZTNA is not just an option; it’s a necessity. It’s the evolution of cybersecurity, ensuring that your hospital’s data stays safe, secure, and only in the right hands.
And let’s face it, in a world where cyber threats are more slippery than a wet bar of soap, ZTNA is the steady hand that keeps your digital ecosystem safe and sound.
In cybersecurity, this is a game-changer. Zero Trust doesn’t just give a nod and a wink at anyone trying to access your network; it asks for their ID, password, and probably what they had for breakfast!
The Evolution of ZTNA
Remember the old days of perimeter-based security? That’s like building a fortress with high walls but not worrying about what happens inside.
Zero Trust, on the other hand, is like having a security guard at every door and window, constantly asking, “Who are you, and why are you here?” It’s about securing each access point and every data transaction – because in this digital age, threats can be as sneaky as a cat in a yarn store.
And why is this especially crucial for hospitals?
Imagine your hospital as a digital treasure chest. This chest doesn’t just have gold; it has something far more valuable – patient data.
Cybercriminals are like modern pirates, and hospitals are their favorite ships to attack.
That’s why Zero Trust is not just important; it’s essential. It’s like having a digital immune system, always on alert, making sure patient data is as safe as a baby in a mother’s arms.
But wait, there’s more!
With great data comes great responsibility. Zero Trust aligns perfectly with all those complex regulatory requirements.
Think of it as the rule-abiding citizen of the cybersecurity world. It doesn’t just protect patient data; it ensures that data is treated with the respect and privacy it deserves, meeting all legal standards.
So, in the end, Zero Trust is not just a security model; it’s your hospital’s digital knight in shining armor!
ZTNA: The Heart of Zero Trust in Healthcare
Think of ZTNA as the vigilant gatekeeper in the realm of healthcare cybersecurity.
It’s not just about locking the doors; it’s about knowing who’s at the door and why they need to come in. ZTNA meticulously controls access to your hospital’s digital resources by checking the ID badge of every user and their devices.
It’s like a bouncer at a club, ensuring only the VIPs (verified identities) get access, and always with just the right level of access they need – nothing more, nothing less.
Key Features of ZTNA in Healthcare Settings
ZTNA brings to the table some nifty tricks like multi-factor authentication (MFA) and continuous monitoring.
MFA is like a secret handshake; it makes sure the person logging in is who they claim to be.
Continuous monitoring, on the other hand, is like having a hawk-eyed guardian that never sleeps, always watching over the network to ensure nothing fishy goes on.
Implementing Zero Trust in Hospitals
Steps to ZTNA Adoption In Clinics
Implementing Zero Trust in a hospital is a bit like solving a puzzle.
First, you need to take a good hard look at the existing IT infrastructure. It’s about identifying the crown jewels – the sensitive data – and then setting up the right controls to protect them.
This process is like conducting a thorough health check-up of your hospital’s IT environment and prescribing the best security measures.
Overcoming Challenges in ZTNA Implementation
Of course, no major change comes without its hurdles. Integrating legacy systems into this new, modern framework can be like teaching an old dog new tricks – challenging but not impossible. And let’s not forget about the human factor.
Ensuring staff adapt to new security protocols is akin to training your team for a digital marathon. It requires patience, training, and a bit of cheerleading to get everyone across the finish line to a more secure digital future.
Enhanced Security and Protection For Medical Institutions
Imagine if your hospital’s data was guarded like Fort Knox. That’s what Zero Trust and ZTNA do – they turn your digital assets into a fortress.
With Zero Trust, it’s not just about putting up a big wall; it’s more like having a security guard at every door, window, and air vent.
This approach ensures that even if a cyber-criminal were as sneaky as a cat in a room full of rocking chairs, they’d still get spotted.
The result? A dramatic plunge in the risk of data breaches, making your hospital’s data as safe as grandma’s secret cookie recipe.
![The Future of Data Security & Enhanced Patient Care Enhanced Security and Protection For Medical Institutions with Zero Trust Network Access [ZTNA]](https://consltek.com/wp-content/uploads/2024/05/image10.802x0-is.png)
Zero Trust: The Bouncer of Digital Access For Improved Access Management
Now, let’s talk about managing who gets into the digital party.
Zero Trust acts like the world’s strictest bouncer, only letting in guests with the right credentials. It’s like having a VIP list for your hospital’s data resources.
This system makes sure that doctors only access what they needs for his patients and doesn’t accidentally wander into the financial records.
It’s about giving the right keys to the right people, significantly limiting the chaos that could ensue if someone’s credentials were stolen.
ZTNA: Playing by the Rules For Acing Regulatory Compliance
Lastly, let’s not forget the ever-looming presence of regulations like HIPAA. In the world of healthcare, staying compliant isn’t just nice; it’s necessary.
Zero Trust is like that rule-abiding, straight-A student who helps keep your hospital on the dean’s list of regulatory compliance.
By implementing robust security measures, Zero Trust ensures that patient data is treated with the utmost respect and care, keeping you in the good books of regulatory bodies.
Zero Trust and ZTNA are not just security measures; they are the superheroes of the healthcare IT world, keeping your data safe, access controlled, and compliance on point.
Zero Trust in Action: No More “Open Door” Policy In Healthcare Facilities
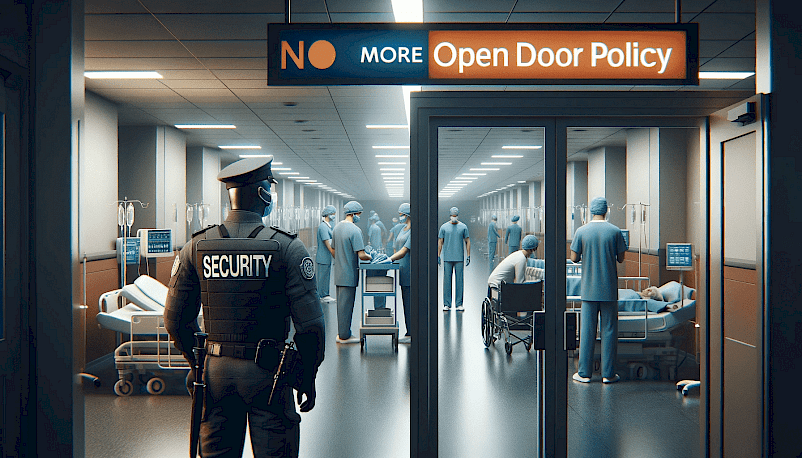
Gone are the days when hospitals operated on a digital “open door” policy. Let’s dive into how real-world hospitals have turned the tide by embracing Zero Trust strategies. Imagine a hospital where even the virtual doors are as guarded as the pharmacy’s medicine cabinet.
Scenario 1: The Hospital That Said “Not on My Network!”
Picture a hospital that’s like a digital all-you-can-eat buffet for cyber threats.
Then, enter Zero Trust. This hospital goes from “Please, come in!” to “Not so fast, who are you?” in their network security.
They implemented stringent verification processes, ensuring that every byte of data was as protected as the secret recipe of the cafeteria’s famous chilli.
The result? A dramatic drop in data breaches and a significant boost in patient trust.
Scenario 2: The Little Hospital That Could… Defend Itself
Next, let’s look at a smaller hospital. They may not have had the biggest budget, but their Zero Trust implementation was as mighty as a nurse with a double espresso.
By ensuring strict access control and continuous monitoring, this little hospital shows that size doesn’t matter when it comes to cybersecurity.
Now, their data is locked down tighter than the last jelly donut in the break room.
The Takeaway: Zero Trust, Maximum Security
These scenarios prove that Zero Trust isn’t just a buzzword; it’s a digital security revolution. Whether big or small, hospitals implementing Zero Trust strategies are like fortresses in the cyber world.
They show that with the right approach, keeping patient data safe isn’t just a dream; it’s a reality, as achievable as finishing your paperwork before the end of the shift.
The Future is Now: AI Meets Zero Trust In Healthcare
Welcome to the future of healthcare cybersecurity, where AI and Zero Trust are the new power couple. Imagine a world where your hospital’s security system is smarter than that phone in your pocket – that’s what we’re talking about here.
AI: The Brain Behind the Trust Brawn
Zero Trust has been like the burly security guard at the hospital’s digital door, but now it’s getting an upgrade – a brain, courtesy of AI.
This means your security system won’t just be flexing muscles; it’ll be flexing neurons too.
AI in Zero Trust is like having Sherlock Holmes join your security team. It’s not just about keeping the bad guys out; it’s about smartly predicting their next move.
Machine Learning: The Security Whisperer
Now, let’s add machine learning to the mix. This is where your security system learns from every attempt to breach it, getting wiser and stronger, like a superhero gaining powers from every battle.
It’s like your hospital’s digital defense system goes to the gym every day – it just keeps getting better.
A Peek into 2024 and Beyond
As we look towards 2024, this isn’t just a fantasy. The integration of AI and machine learning with Zero Trust is set to revolutionize healthcare cybersecurity.
We’re talking about a system so smart, it could probably do your taxes and walk your dog. But instead, it’s keeping patient data safer than ever before.
So, gear up! The future of healthcare cybersecurity is bright, intelligent, and ready to take on whatever cyber threats come its way. It’s like your hospital’s network is getting a superhero upgrade, cape and all!
Cato SASE Cloud: The Digital Doctor for Hospital Networks
Welcome to the world of Cato SASE Cloud, where hospital cybersecurity gets a major upgrade! Think of it as the digital equivalent of a superhero nurse, always ready to protect and serve.
ZTNA: The Secret Sauce For Clinic Cybersecurity
Let’s talk about Zero Trust Network Access (ZTNA) – the secret sauce in Cato’s cybersecurity recipe.
ZTNA is like the hospital’s bouncer, ensuring that only verified and authorized users and devices can access its digital resources.
It’s like having a security checkpoint at every door and window of your digital hospital.
Securing Every Nook and Cranny
Cato SASE Cloud with ZTNA is not just about guarding the front door. It’s about securing every nook and cranny of the hospital’s network.
Whether it’s telework, SaaS, IaaS, or mobile terminals, Cato’s got it covered. It’s like having a security guard for every patient room, supply closet, and even the cafeteria!
Battling Insider Threats
What about the threats that come from inside the hospital?
Worry not! Cato SASE Cloud extends its ZTNA capabilities to protect against insider threats too. It’s like having a secret agent within your walls, keeping an eye on everything that moves.
Rapid Deployment: Zero Touch, Full Security
And the best part? Implementing Cato SASE Cloud is as quick as setting up an IV drip.
With zero touch and self-service provisioning, hospitals can onboard users and locations in minutes, anywhere in the world. It’s like giving your hospital a cybersecurity makeover overnight.
The Bottom Line: Safe Data, Happy Patients
In summary, Cato SASE Cloud brings hospitals into the future of cybersecurity with its comprehensive ZTNA approach.
It’s the guardian angel for hospital networks, ensuring that patient data is as safe as a band-aid on a boo-boo.
Wrapping It Up: The Cybersecurity Prescription for Healthcare Providers
As we come to the end of our digital health journey, let’s talk about why hospitals need to embrace Zero Trust like a doctor embraces hand sanitizer.
In the world of relentless cyber threats, going Zero Trust is not just a ‘good-to-have’ – it’s as essential as caffeine in the ER.
Zero Trust: Not Just a Trend, But a Healthcare Staple
Zero Trust in healthcare is like having a super-smart immune system for your hospital’s network. It doesn’t just trust anyone waltzing in; it’s the equivalent of a nurse with a “why are you here?” look.
This approach is crucial because, let’s face it, cyber threats are evolving faster than bacteria on a petri dish.
Cato SASE Cloud: The Stethoscope for Your Network
Now, enter Cato SASE Cloud – the stethoscope for your network’s health. It’s the perfect fit for Zero Trust Network Access (ZTNA) at hospitals. Why?
Because Cato SASE Cloud doesn’t just protect; it adapts. It’s like having a security system that’s also a quick-learning med student, constantly evolving to tackle the latest cyber bugs.
The Final Diagnosis: Embrace or Brace
In conclusion, for hospitals, embracing Zero Trust with tools like Cato SASE Cloud is not just a smart move; it’s a survival strategy. It’s like choosing between a fortified, germ-free operating room and a risky, open-air surgery in the park.
So, let’s button up those lab coats and step into a future where hospital networks are as secure as the vaults of the CDC!
9 frequently asked questions on ZTNA for Hospitals
-
What is Zero Trust Network Access (ZTNA) and how does it enhance hospital cybersecurity?
Imagine ZTNA as the hospital’s digital doorman who’s got trust issues – and rightfully so! It’s a security approach that verifies every user and device before granting access to the hospital’s network.
Think of it like a nurse double-checking patient IDs before giving out medications. For hospitals, this means an extra layer of security, ensuring patient data is as guarded as the last piece of cake in the staff break room.
-
How does ZTNA differ from traditional network security approaches in the healthcare sector?
Traditional network security in hospitals was like leaving the front door open but locking the medicine cabinet.
It relied heavily on securing the network perimeter.
ZTNA, on the other hand, is like putting a lock on every door and drawer. It doesn’t just guard the perimeter; it checks the credentials at every access point within the network, making sure that only the right people have the key to the right doors.
-
Can ZTNA help medical institutions comply with healthcare data privacy regulations like HIPAA?
Absolutely! Implementing ZTNA is like having a compliance officer on steroids. By controlling who accesses what data and when, ZTNA aligns perfectly with HIPAA’s strict privacy rules.
It’s like having a digital bodyguard for patient data, ensuring no unauthorized peeks into sensitive information, thus keeping the hospital on the right side of compliance and far away from those scary HIPAA violation fines.
-
How does ZTNA manage access to sensitive patient data and hospital records?
ZTNA is like the ultimate gatekeeper for a hospital’s digital domain. It manages access to sensitive patient data by implementing a “trust no one, verify everyone” policy.
Each time someone or something tries to access the network, ZTNA checks their credentials and context. Imagine it as a digital receptionist who not only checks your ID but also double-checks why you’re there and if you’re supposed to be there at that time.
This ensures that only authorized individuals get their hands on patient records, keeping the data as secure as the formula for a secret sauce.
-
What are the steps to implement ZTNA in a hospital’s existing IT infrastructure?
Implementing ZTNA in a hospital isn’t rocket science, but it does need a methodical approach. Here’s the game plan:
- Define Objectives: Collaborate with business leaders to align ZTNA with the hospital’s security needs.
- Assess Current Infrastructure: Take stock of existing network and security setups.
- Plan the Integration: Map out how ZTNA will fit into the existing system.
- Focus on Identity and Access: Implement identity verification and access control mechanisms.
- Roll Out in Phases: Start with less critical systems to test and adjust before full-scale implementation.
- Train Staff: Educate hospital staff about the new protocols to ensure smooth operation.
- Monitor and Adapt: Continuously monitor the system and adapt as needed for evolving threats and needs.
-
How does ZTNA address the challenges of remote access for healthcare professionals?
With more healthcare professionals working remotely, ZTNA steps in like a tech-savvy genie. It offers secure remote access by verifying user identity and the security status of their devices before allowing access.
This means doctors and nurses can securely access patient data from anywhere, be it from home or a coffee shop. ZTNA ensures that remote access is as safe as in-hospital access, making telemedicine and remote consultations as secure as a vault.
-
Can ZTNA be integrated with other clinical security systems, such as firewalls or intrusion detection systems?
Absolutely! ZTNA plays well with others. It can be integrated seamlessly with existing hospital security systems like firewalls and intrusion detection systems.
Think of ZTNA as the new kid on the block who quickly becomes friends with everyone. By integrating ZTNA, hospitals can create a comprehensive security posture, where ZTNA adds an extra layer of identity and access management on top of the traditional security measures.
-
How does ZTNA handle emergency access for healthcare staff in critical situations?
ZTNA understands the need for speed, especially in emergencies. It’s designed to handle urgent access without compromising security.
In critical situations, ZTNA can provide rapid, secure access to healthcare staff based on predefined emergency protocols. It’s like having a digital fast lane for emergencies, ensuring that healthcare professionals get immediate access to the resources they need, just like an ambulance breezing through traffic.
What training is required for hospital staff to effectively use a ZTNA system?
Rolling out ZTNA in a hospital does call for some staff training, but it’s nothing too daunting. The training typically covers understanding the principles of Zero Trust, the procedures for secure access, and how to handle common scenarios.
It’s a bit like teaching staff a new hygiene protocol – a series of straightforward steps they need to follow to ensure the digital health and safety of patient data.
With clear guidance and some practice, hospital staff can become adept at using ZTNA systems efficiently.
-
How does ZTNA contribute to overall patient care and hospital service delivery?
Zero Trust Network Access (ZTNA) contributes significantly to enhancing patient care and hospital service delivery in several key ways:
- Enhanced Data Security: ZTNA fortifies the protection of sensitive patient data. By ensuring that access to this data is tightly controlled and monitored, ZTNA helps maintain patient privacy and trust, which are crucial elements of patient care.
- Improved Accessibility for Healthcare Providers: ZTNA facilitates secure remote access for healthcare professionals. This means doctors and nurses can securely access patient records and critical systems from anywhere, enabling better coordination and faster decision-making, especially in emergency situations.
- Reduction in Data Breach Risks: By minimizing the risk of data breaches, ZTNA helps maintain the integrity of hospital services. Patients’ health records are kept safe, ensuring that healthcare decisions are based on accurate and unaltered information.
- Compliance with Health Regulations: ZTNA helps hospitals stay compliant with healthcare regulations like HIPAA, which require the safeguarding of patient data. This compliance is critical for avoiding legal issues and fines, thereby maintaining smooth hospital operations.
- Efficient IT Operations: With ZTNA, IT teams can better manage who has access to what data and when. This streamlined access control reduces the burden on IT resources, allowing for more focus on enhancing patient care technologies and services.
In summary, ZTNA plays a pivotal role in supporting the digital backbone of modern healthcare institutions, ensuring secure, efficient, and compliant operations that ultimately translate to better patient care and service delivery.